Highlights from DEFCON 25
DEFCON 25 is now over. The largest hacking conference in the world continues to grow larger each year. Previous years there were 18-22,000 attendees. This year over 23,000 people made it to Ceasars Palace for the talks, workshops, parties, and social activities.
Here are some notable highlights from the event.
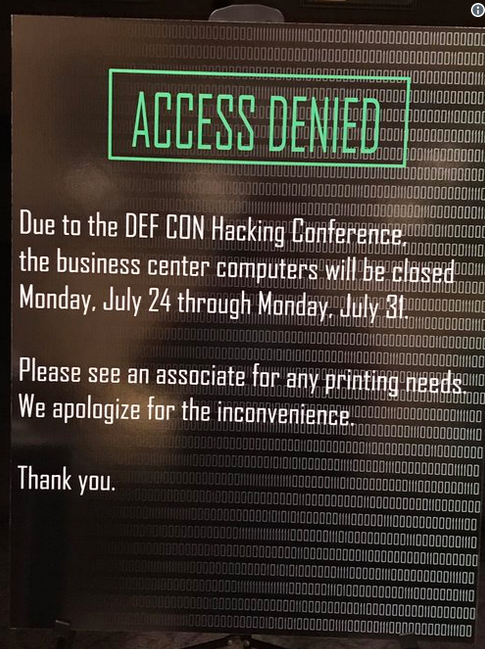
On Lockdown
When DEFCON rolls into town, some shops close their shutters to avoid potential threats. In previous years we’ve seen the neon signs become blue screened, and many other pranks and shenanigans. This year we saw this.
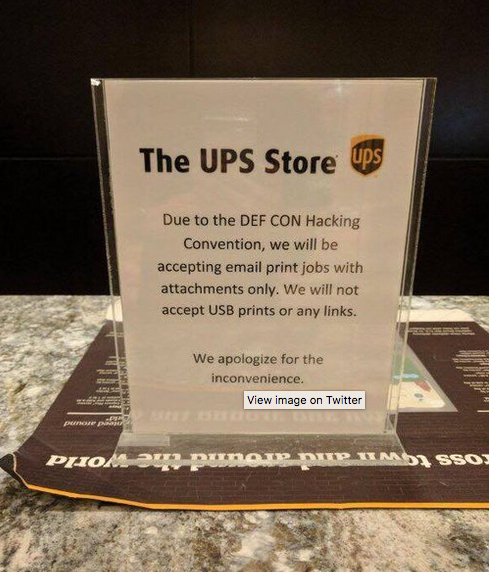
It doesn’t seem like UPS gets it.
Voting machines not as secure as you think.
The big news this event is the voting machines. A total of 30 different voting machines were brought to the conference to test their security, and hilarity ensued.
The machines were put on the network and people were encouraged to attack them through the network. In the first 90 minutes, the first voting machine was popped. And soon additional voting machines were also found to have weak security.
It seems these machines weren’t updated with patches and had additional weak security controls. When one attendee got into a machine they found the machine was still holding 650,000 voter names and votes. This was a machine that was purchased on ebay. So not only are the machine weak the data on them isn’t being looked after properly. Another machine was found to be able to remotely change the votes on the system by a hacker.
Many attendees were saying the slot machines in the casino’s are more secure than the voting machines we use to run our democratic way of life. And this is true. The slot machines undergo strict audits, not only by the game makers, but also by the gaming board. Slot machines have a long history of being secure and bug free. We all hope this is an eye opener for voting machine companies and government to take the security of these more seriously.
Is a Car Wash Secure?
Security researchers Billy Rios of WhiteScope Security and Jonathan Butts of QED Secure Solutions gave a talk that demonstrates how they can remotely take over a car wash. In this demonstration they were able to close the bay doors of the car wash and change the behavior of the spray jets. They did this through a network based attack where they could have been on the other side of the globe.
One reason someone might want to do this is to physically harm or trap a person in a car wash. By letting the bay doors down at the right time it can smash the car and driver which can severely impact the car and driver.
To be safe, maybe avoid car washes that have automatic bay doors that can trap you inside.
Work Badges Easily Cloned
At DEFCON 18 I first saw someone close a security badge. The ones you might get at work, or give you access to a gated community or something. The equipment then was clunky and slow. You needed to be almost touching the badge and it would take a while.
The technology has improved tremendously for cloning these badges. A talk was given by Dennis Maldonado that demonstrated he can read the data of a badge from 2 feet away and then send that another 30 feet away to be processed.
He was able to take it a step further and make the whole thing trigger from his Pebble watch and an Android app.
To avoid being attacked like this and having your badge cloned without you knowing it, keep it in a safe place when not using it and consider using and RF blocker wallet to store it in.
Safe Cracking Robot
Sparkfun founder Nathan Seidle built a combination lock cracking robot.
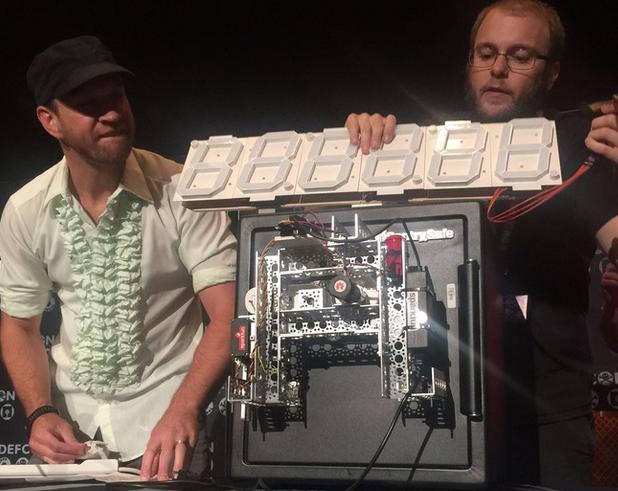
To demonstrate it, he bought a safe from Home Depot, attached his robot to it, and within 30 minutes the robot cracked the safe. The robot would rotate the knob back and forth feeling for just the right tension to open the safe. It needed to try numerous combinations to finally get it, but it was able to do it rapidly enough to be able to demonstrate it live on stage.
This certainly makes the future of safes and locks an interesting concept. This is something you might see in a sci fi movie, and is now becoming a reality.